Tài liệu giới thiệu GRC của doanh nghiệp
Quote from bsdinsight on 25 November 2023, 15:34
Introduction
This document is the property of Vakrangee Limited and is for use only by Vakrangee Limited or any of its group Companies. It must not be copied, disclosed, circulated or referred to in correspondence with external parties or discussed with any other party other than for any regulatory requirements without prior written consent from the Management and the Anti- Fraud Committee.
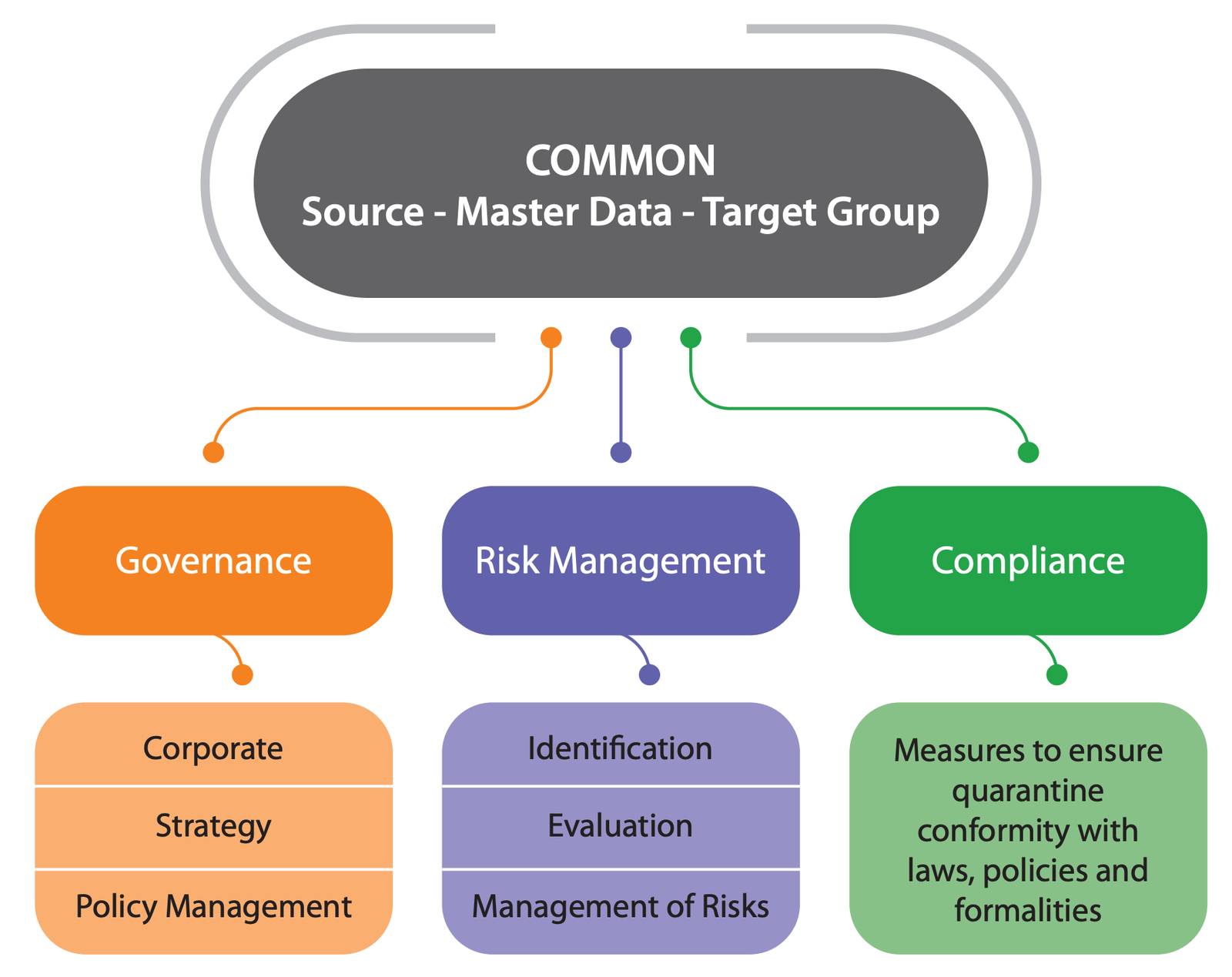
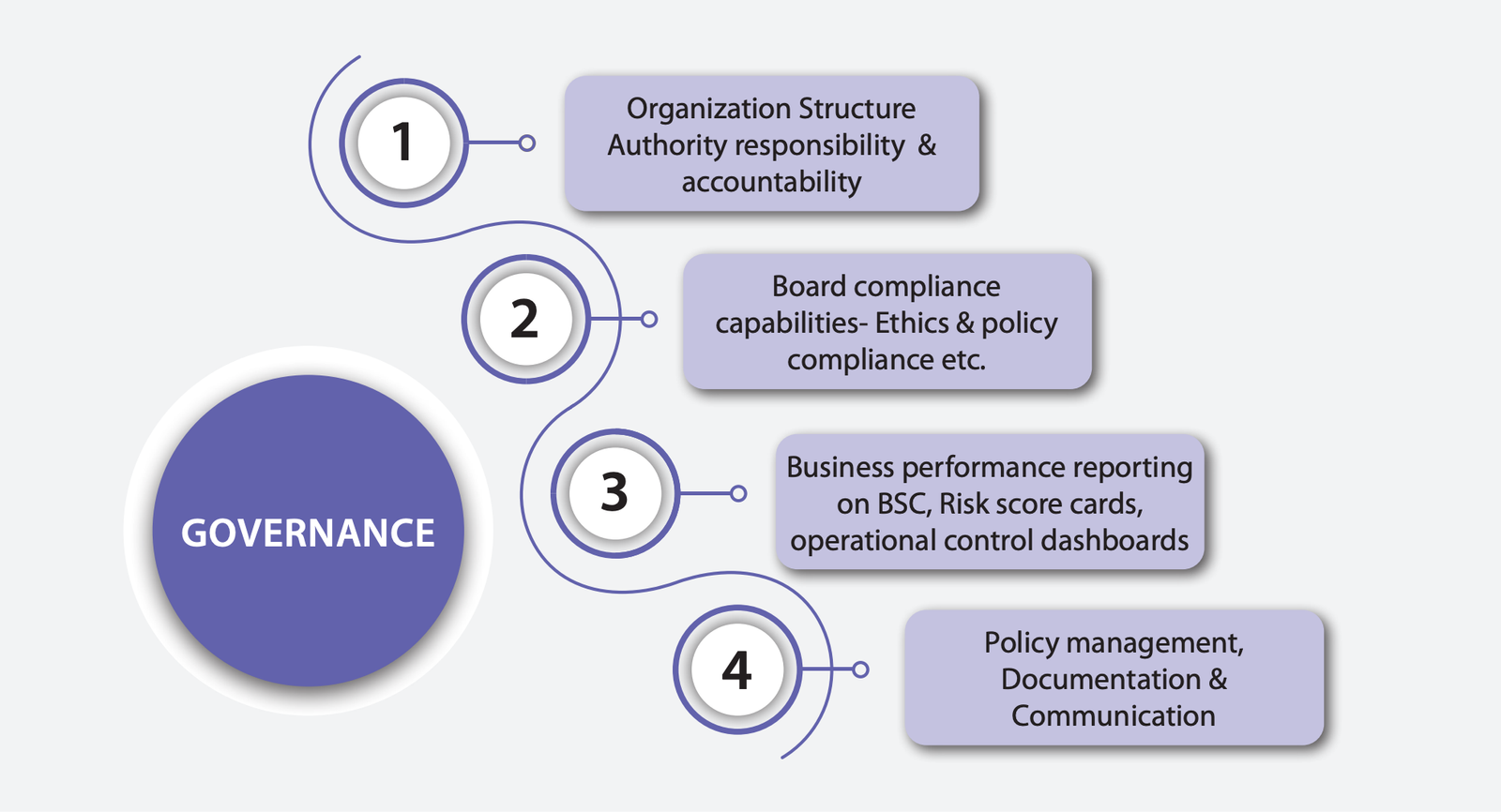
Governance
Ensuring that organizational activities, like managing IT operations, are aligned in a way that supports the organization’s business goals.
We have established a Corporate Security and Compliance Team (CSC) made up of key personnel whose responsibility is to identify areas of security and compliance concern across the organization and act as the first line of defence in enhancing the appropriate security and compliance posture. This team reports to the Chief Technology Officer.
The team comprises the workforce who are knowledgeable in legal cross-regulation, policy, products, and IT, and are interested in ensuring five of the trust principles—confidentiality, integrity, availability, privacy, and security—with regard to data protection by law, compliance, and standards across the organization. The Chief Technology Officer has assigned the responsibilities and authority to Data Protection Officer for overseeing and maintaining information security and compliance as per the standard and industry best practices.
The governance of these programs is performed by the Corporate Security and Compliance Committee, consisting of executives and other department heads across the organization.
Risk
Making sure that any risk (or opportunity) associated with organizational activities is identified and addressed in a way that supports the organization’s business goals. In the IT context, this means having a comprehensive IT risk management process that rolls into an organization’s enterprise risk management function.
We have established and implemented robust Risk Management Procedure and Process in place and conduct periodic risk assessments for the organization using the baseline methodology based on ISO 27001 standard framework with cross-reference with ISO 9001, PCI DSS and industry best practices.
We are not willing to accept any risk that might damage customer trust. In addition, any risks that threaten to make us non-compliant to regulations and standard. Risk Treatment Plan involves prioritizing, evaluating, and implementing appropriate controls as per the risk computation.
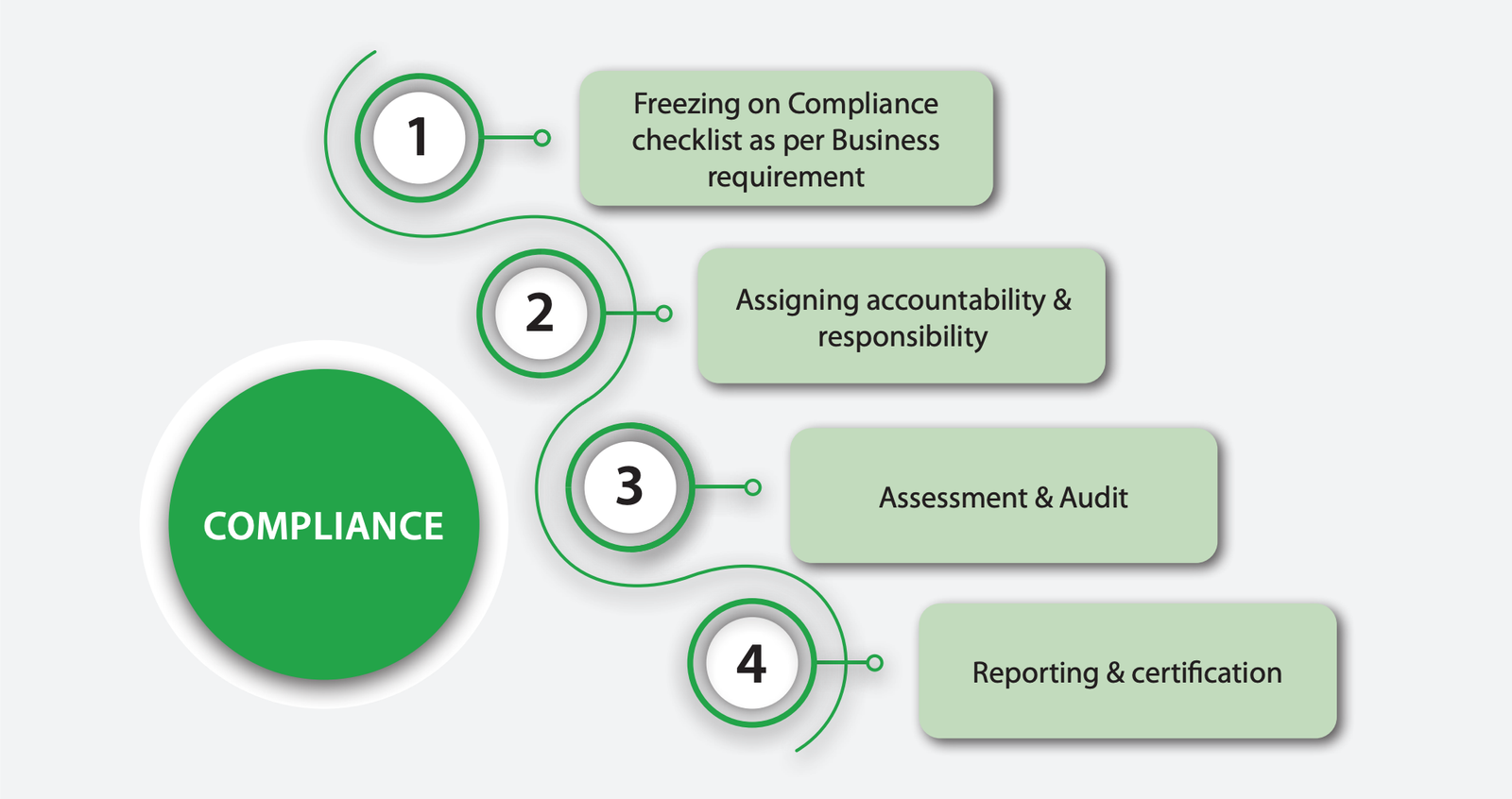
Compliance
Making sure that organizational activities are operated in a way that meets the laws and regulatory requirements impacting the systems. In the IT context, this means making sure that IT system, and the data contained in those systems, are used and secured properly.
We have established a formal Compliance Policy and Procedure which addresses aspects of compliance required to be adhered to and fulfilled with respect to our Information Security Policies. This policy also addresses the legal and compliance requirements pertaining to relevant statutory legislation, and contractual and regulatory obligations which we are supposed to adhere to in order to protect its documents, records, and assets, thereby preventing the misuse of information processing facilities. Such efforts would help us establish, maintain, and sustain the desired information security and privacy posture aligned with our strategic business plan, based on the best practices, standards, and principles.
We are committed to and conducts its business activities lawfully and in a manner that is consistent with its compliance obligations.
We have been identifying all relevant regulatory and legislative requirements in lien of its contractual requirements and organization’s operational requirements and defining, documenting, and updating it on a regular basis.
All records, as mandated by statutory/legal/regulatory authorities in India or of foreign origin, for which we are responsible for compliance, shall be protected from intentional or unintentional damage through natural causes.
Đọc và tải tài liệu tại đây
[dflip id="96409" ][/dflip]
Introduction
This document is the property of Vakrangee Limited and is for use only by Vakrangee Limited or any of its group Companies. It must not be copied, disclosed, circulated or referred to in correspondence with external parties or discussed with any other party other than for any regulatory requirements without prior written consent from the Management and the Anti- Fraud Committee.
Governance
Ensuring that organizational activities, like managing IT operations, are aligned in a way that supports the organization’s business goals.
We have established a Corporate Security and Compliance Team (CSC) made up of key personnel whose responsibility is to identify areas of security and compliance concern across the organization and act as the first line of defence in enhancing the appropriate security and compliance posture. This team reports to the Chief Technology Officer.
The team comprises the workforce who are knowledgeable in legal cross-regulation, policy, products, and IT, and are interested in ensuring five of the trust principles—confidentiality, integrity, availability, privacy, and security—with regard to data protection by law, compliance, and standards across the organization. The Chief Technology Officer has assigned the responsibilities and authority to Data Protection Officer for overseeing and maintaining information security and compliance as per the standard and industry best practices.
The governance of these programs is performed by the Corporate Security and Compliance Committee, consisting of executives and other department heads across the organization.
Risk
Making sure that any risk (or opportunity) associated with organizational activities is identified and addressed in a way that supports the organization’s business goals. In the IT context, this means having a comprehensive IT risk management process that rolls into an organization’s enterprise risk management function.
We have established and implemented robust Risk Management Procedure and Process in place and conduct periodic risk assessments for the organization using the baseline methodology based on ISO 27001 standard framework with cross-reference with ISO 9001, PCI DSS and industry best practices.
We are not willing to accept any risk that might damage customer trust. In addition, any risks that threaten to make us non-compliant to regulations and standard. Risk Treatment Plan involves prioritizing, evaluating, and implementing appropriate controls as per the risk computation.

Compliance
Making sure that organizational activities are operated in a way that meets the laws and regulatory requirements impacting the systems. In the IT context, this means making sure that IT system, and the data contained in those systems, are used and secured properly.
We have established a formal Compliance Policy and Procedure which addresses aspects of compliance required to be adhered to and fulfilled with respect to our Information Security Policies. This policy also addresses the legal and compliance requirements pertaining to relevant statutory legislation, and contractual and regulatory obligations which we are supposed to adhere to in order to protect its documents, records, and assets, thereby preventing the misuse of information processing facilities. Such efforts would help us establish, maintain, and sustain the desired information security and privacy posture aligned with our strategic business plan, based on the best practices, standards, and principles.
We are committed to and conducts its business activities lawfully and in a manner that is consistent with its compliance obligations.
We have been identifying all relevant regulatory and legislative requirements in lien of its contractual requirements and organization’s operational requirements and defining, documenting, and updating it on a regular basis.
All records, as mandated by statutory/legal/regulatory authorities in India or of foreign origin, for which we are responsible for compliance, shall be protected from intentional or unintentional damage through natural causes.
Đọc và tải tài liệu tại đây